Ensuring Business Continuity with High-Availability Network Solutions
Even when a reliable and robust network infrastructure is put in place, multiple hazards can occur. Hacking, sudden surges, hardware accidents, natural disasters, human error... All these factors are likely to cause breakdowns and weigh on the productivity of companies. Many of them therefore choose the peace of mind offered by a high-availability network. But, how do you achieve this level of reliability?
Availability, a key factor in the SLA
Let's start by explaining the concept of availability. This measure is generally expressed as a percentage: it corresponds to the time during which a service is effectively accessible divided by the total duration considered. In general, we speak of high IT availability when this value exceeds 98 or 99% (or more, depending on the degree of requirement).
Unavailability at the network level can have serious consequences on a company. It can prevent teams from working, freeze customer purchases or interrupt production. Therefore, some applications have high availability requirements in order to meet critical reliability needs.
This is why this criterion plays an important role in the Service Level Agreement (SLA) between a supplier and a customer. This document lists the various service quality objectives to be achieved by the IT service provider. In addition to this characteristic, the SLA can also include response time, user satisfaction, etc.
How to ensure the high availability of a network?
In order to limit as much as possible the risks of unavailability of a company's IT network (WAN, LAN and/or WiFi), several levers can be activated. Here are some of the major principles on which they are based:
Firstly, the technique known as " load balancing " can promote a high availability architecture. It consists of intelligently distributing flows over several devices in order to avoid overloading them.
“ Clustering " is a similar approach. It involves pooling several devices, such as servers, which function as a single system. This type of infrastructure, especially in the context of a network, allows for load balancing and better reliability.
Finally, " failover " occurs in the event of a major anomaly. It aims to redirect a request from one server to another, when the first is confronted with a failure. This gives time to identify the cause of the malfunction and to solve the problem.
On which part of the network infrastructure does high availability apply?
As you can see from the various solutions described above, redundancy plays a key role in high availability. It offers precious reactivity, as one equipment can replace another in case of a malfunction. However, it is not enough to duplicate a machine to obtain a perfectly resilient system. It is also necessary to establish operating rules, based on the previous principles (load balancing, clustering, failover, etc.), but also to reproduce the network redundancy at different levels.
For starters, it is in a company's best interest to provide redundancy for its professional Internet access. For example, if this access is based on a single collection link, the organization could be paralyzed in the event of an incident related to this Internet access. Therefore, it may be useful to provide additional access, either through the same technology or through different technology.
Ex: Rather than opting for a single 200 Mbps fiber optic link, I will opt for two 100 Mbps fiber optic links provided by different collection operators. I will therefore have 200 Mbps in normal times and in case of an incident on one of my fiber inputs, my company will always have 100 Mbps available.
-UK.jpg?width=583&name=illustration-lien-secours-(redondance)-UK.jpg)
The principle of Internet access redundancy illustrated
Then, a switch redundancy is also judicious for the high availability of the local network (also called "LAN"). These devices act as switches, directing data flows to the right recipients. Their importance is therefore crucial within the infrastructure. Hence the interest in "redundancy".
Ex: I choose to build my local network core around stacked switches. If a malfunction occurs on one of them, the core network will still be functional and so will my local network.
Finally, the same method can be applied to a WiFi network. It is thus possible to cover the same area with two terminals. When one of them stops working, the other one continues to offer sufficient connectivity in order to avoid any service interruption.
Ex: Instead of defining the right number of terminals to cover a space, I will increase this number by 30 to 40% and position them so that they do not interfere with each other. This close meshing will allow a WiFi terminal to take over from another one in case of malfunction.
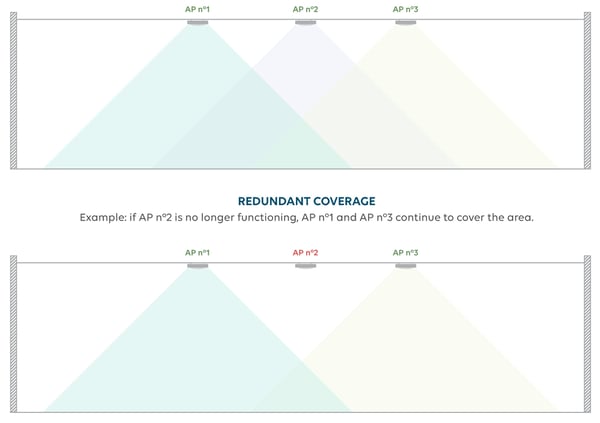
Visual representation of WiFi redundancy
(does not illustrate the interference issues to be considered when setting up the terminals)
- Wifi (43)
- Hotel Industry (18)
- Digital Workplace (14)
- Behind the scenes (8)
- IPTV - Signage (8)
- Optical fibre (7)
- Retail (6)
- Green-IT (5)
- Education (3)
- Healthcare (2)
- Cybersecurity (1)
- General (1)
- Hospitality (1)
- PBSA (1)
- Student Accommodation (1)
- Telephony (1)
- Tips and tricks (1)
- Tourism (1)
- Wifirst (1)
You May Also Like
These Related Stories

Enhancing PBSA Connectivity: Solving 5 Key Challenges with Wifirst

Enhancing Productivity and Connectivity in Coworking Spaces with WiFi
